Unfolding now: news.ycombinator.com/item?id=3…
- openwall.com/lists/oss-securit…
- github.com/tukaani-project/xz/…
An incredibly technically complex #backdoor in xz (potentially also in libarchive and elsewhere) was just discovered. This backdoor has been quietly implemented over years, with the assistance of a wide array of subtly interconnected accounts:
- github.com/tukaani-project/xz/…
- bugs.debian.org/cgi-bin/bugrep…
- github.com/jamespfennell/xz/pu…
The timeline on this is going to take so long to unravel
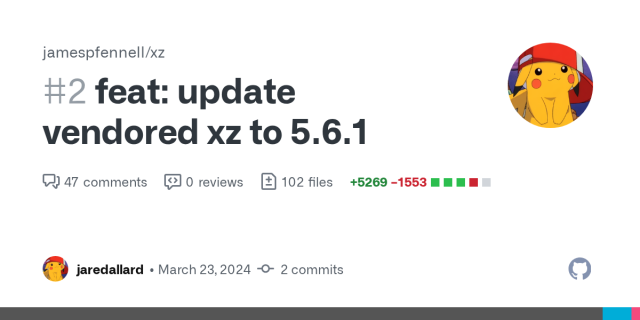
feat: update vendored xz to 5.6.1 by jaredallard · Pull Request #2 · jamespfennell/xz
Updates the vendored version of xz to be 5.6.1. Also updates the vendor script to support the addition of SPDX-License-Identifier headers into some files.GitHub
This entry was edited (1 year ago)
Evan B🥥ehs
in reply to Evan B🥥ehs • • •boehs.org/node/everything-i-kn…
I have begun a post explaining this situation in a more detailed writeup. This is updating in realtime, and there is a lot still missing.
#security #xz #linux
Everything I know about the XZ backdoor
boehs.orgEvan B🥥ehs
in reply to Evan B🥥ehs • • •Glyph
in reply to Evan B🥥ehs • • •Re: [xz-devel] XZ for Java
www.mail-archive.comGlyph
in reply to Glyph • • •