🆕 blog! “A small contribution to curl”
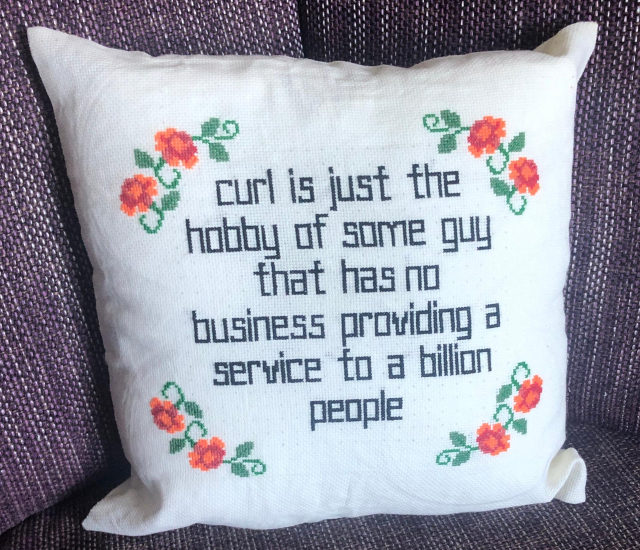
The venerable curl is one of the most fundamental pieces of code in the modern world. A seemingly simply utility - it enables other programs to interact with URls - it runs on millions of cars, is inside nearly every TV, used by billions of people, and is even in use on Mars.
And, as of last week, features a small contribution by…
👀 Read more: shkspr.mobi/blog/2025/02/a-sma…
⸻
#curl #documentation #OpenSource

The venerable curl is one of the most fundamental pieces of code in the modern world. A seemingly simply utility - it enables other programs to interact with URls - it runs on millions of cars, is inside nearly every TV, used by billions of people, a…
Terence Eden’s Blog