Why did the #curl #CVE202338545 vulnerability hide from static analysis tools?
The main reason for this is the type of code structure in question. In general state engines are quite difficult for static analysis tools, since as the name implies the state of the various variables depend on runtime state changes.
The code attempts to determine whether it is safe to use the provided host name for remote resolution. Since the code does not function correctly with host names longer than 255 characters, it falls back to using “socks5://” protocol (local name resolution) if the host name is longer. When the name is too long, the code forces “local name resolution” by setting “socks5_resolve_local” variable to TRUE.
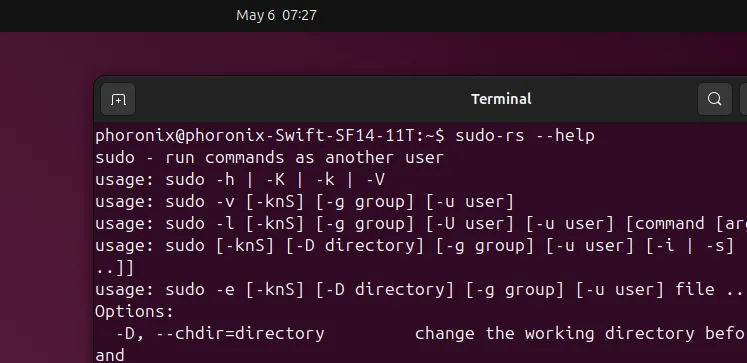
Unfortunately this “socks5_resolve_local” variable isn’t stored in the “socks_state” structure as it should have been. For each state “step” the initial value for the variable is determined with:
bool socks5_resolve_local =
(conn->socks_proxy.proxytype == CURLPROXY_SOCKS5) ? TRUE : FALSE;
The INIT state then set the “socks5_resolve_local” to TRUE if the host name is too long:
/* RFC1928 chapter 5 specifies max 255 chars for domain name in packet */
if(!socks5_resolve_local && hostname_len > 255) {
infof(data, "SOCKS5: server resolving disabled for hostnames of "
"length > 255 [actual len=%zu]", hostname_len);
socks5_resolve_local = TRUE;
}
But this check is *only* done in INIT state. When the state is anything else, the initial value is used.
Now, later CONNECT_RESOLVE_REMOTE state checks if remote name resolution should be used or not:
if(!socks5_resolve_local) {
if (… sx->hostname is literal IPv6 address …) {
… use ipv6 address direct …
}
else if (… sx->hostname is literal IPv4 address …) {
… use ipv4 address direct …
}
else {
socksreq[len++] = 3;
socksreq[len++] = (char) hostname_len; /* one byte address length */
memcpy(&socksreq[len], sx->hostname, hostname_len); /* w/o NULL */
len += hostname_len;
}
}
As “socks5_resolve_local” flag is FALSE for the excessively long hostname the “socksreq” heap buffer will be overflown by the memcpy call.
There is no obvious way for the static analysis tools to determine that “socks5_resolve_local” might be set incorrectly for some of the states. Runtime #fuzzing will find this flaw quite easily, but unfortunately no fuzzing was performed for this specific functionality.
#vulnerability #staticanalysis #infosec