Search
Items tagged with: CURL

support Linux and macOS curl binaries by vszakats · Pull Request #53 · curl/curl-for-win
Add the ability to create Linux and macOS binaries. We are keeping the name curl-for-win though. Non-Windows binaries are experimental at this point and they are not official curl binaries for thes...GitHub
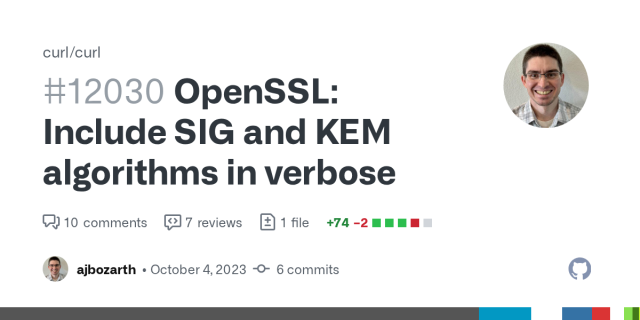
OpenSSL: Include SIG and KEM algorithms in verbose by ajbozarth · Pull Request #12030 · curl/curl
Currently the verbose output does not include which algorithms are used for the signature and key exchange when using OpenSSL. Including the algorithms used will enable better debugging when workin...GitHub
BINDINGS: add V binding by ttytm · Pull Request #12182 · curl/curl
Astonishing how good libcurl works. Thanks a lot for the work that so many projects can build on. The PR adds a link to a V request lib that uses libcurl.GitHub
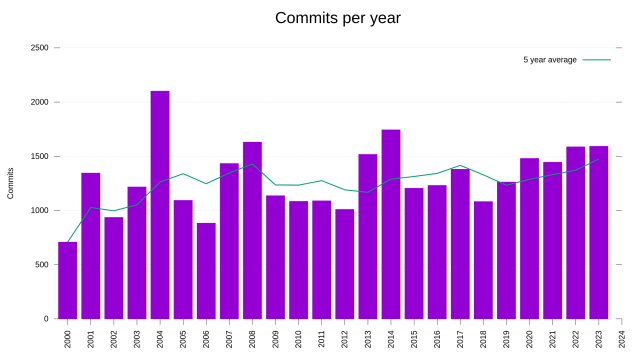
in the #curl project, we have already done more commits in 2023 than any single previous year since 2014. If we manage 152 more commits this year, 2023 will become the most-commits year since 2004, which remains our top year with 2102 commits in a single year.
Things you figure out when you have graphs.
docs: fix function typo in curl_easy_option_next.3 by rilysh · Pull Request #12170 · curl/curl
Hello, When I was reading libcurl docs, I noticed that there's a minor mistake in the curl_easy_option_next example manpage. In that specific example, curl_easy_option_by_next() has been used, howe...GitHub
Brodie speaks up about the AI generated security report crap the #curl project received recently, and I think he does it nicely.
youtu.be/r0-tKuoiagY?si=QjxaFt…

CURL Project Trolled By Fake AI Bug Report
When you're a project as big as curl sometimes you get some weird bug report and recently Daniel Stenberg got a completely AI generated made up report, pleas...YouTube
PlayStation doesn't have getenv() by fffaraz · Pull Request #12140 · curl/curl
Build fails on PlayStation since it doesn't have getenv()GitHub
On this day, six years ago, I was awarded the Polhem Prize for my work on #curl - and went home with a gold medal that was handed to me by the King of Sweden. A night to remember.
Later this afternoon in #Stockholm I will blab #curl (again):
nordicapis.com/sessions/next-l…
Next Level Curl | Nordic APIs
During this talk, Daniel Stenberg will look at some of the most powerful and interesting additions to curl in recent years.Nordic APIs
We disclosed this #hackerone report against #curl when someone asked Bard to find a vulnerability, and it hallucinated together something:
![curl disclosed on HackerOne: [Critical] Curl CVE-2023-38545...](https://fedi.ml/photo/preview/640/464379)
curl disclosed on HackerOne: [Critical] Curl CVE-2023-38545...
## Summary: Curl CVE-2023-38545 vulnerability code changes are disclosed on the internet ## Steps To Reproduce: To replicate the issue, I have searched in the Bard about this vulnerability. It...HackerOne
Latest BASH (version 5.2) and CURL (version 8.4.0) is available for IBM i. 😍
Thank you, IBM!
As always update using yum or ACS.
BASH 5.2 release note: lists.gnu.org/archive/html/bas…
CURL 8.4.0 changelog: curl.se/changes.html#8_4_0
tool_operate: fix links in ipfs errors by lidel · Pull Request #12133 · curl/curl
This is a cosmetic fix of errors returned by cli tool (added in #8805) (URL fragment links generated from headers in https://curl.se/docs/ipfs.html are lowercase)GitHub

Added missing parameter 'lpNumberOfCharsWritten' for WriteConsoleW() by lordmulder · Pull Request #12130 · curl/curl
This is documented as "optional" by Microsoft, I know. But, apparently, this was not optional on older Windows versions! On those version, the function verifiably fails with error ERROR_INVALID_ACC...GitHub
docs/libcurl: fix three minor man page format mistakes by charles2910 · Pull Request #12126 · curl/curl
Hi there, After the last upload of curl to Debian (8.4.0), samueloph noticed some lintian warnings about the manpages: W: libcurl4-doc: groff-message troff::106: warning: macro '..'...GitHub
tool_getparam: Limit --rate to be smaller than number of ms by sohomdatta1 · Pull Request #12116 · curl/curl
Currently, curl allows users to specify absurd request rates that might be higher than the number of milliseconds in the unit (ex: curl --rate 3600050/h http://localhost:8080 does not error out des...GitHub
Good question.
The only person I know that is even remotely into that stuff may be @ncommander.
After all, #backporting #curl to legacy #FreeBSD sounds like the kind of #SoftwareGore and #DigitalMasochism he's likes to showcase on his #YouTube channel...
Anyone happen to know anything about #FreeBSD (legacy) header files and wants to help us out with a #curl build issue?
github.com/curl/curl/pull/1210…
curl.h: only include "osreldate.h" on pre v8 FreeBSD by bagder · Pull Request #12109 · curl/curl
Follow-up to b89789d. This header does not exist in all modern versions. Fixes #12107 Reported-by: Faraz FallahiGitHub
This week many engineering teams are looking for the immensely popular open source library 'curl' in order to get ahead of the CVE-2023-38545 vulnerability. Most of them are NOT going to see it in their SBOM even though they use it.
In this article I walk through why this is, places it might be hiding and questions to ask that can help uncover your use of it.
zebracatzebra.com/oss/curl-is-… #curl #sca #sbom
Curl is seen everywhere except your SBOM, why is it missing even though you use it?, Zebra Cat Zebra
What is curl? curl is an open source command line tool and embeddable library for transferring data over a network.Zebra Cat Zebra
I watched “Mastering the curl command line with @bagder”
It took me more than a week and it was totally worth it!
youtube.com/watch?v=V5vZWHP-Rq…
#curl

Mastering the curl command line with Daniel Stenberg
The slides = https://www.slideshare.net/DanielStenberg7/mastering-the-curl-command-linepdf0:00 Mastering the curl command line0:16 Daniel Stenberg0:36 curl s...YouTube
http2: Safer invocation of populate_binsettings by klyubin · Pull Request #12101 · curl/curl
populate_binsettings now returns a negative value on error, instead of a huge positive value. Both places which call this function have been updated to handle this change in its contract. The way p...GitHub
Next week on "Platform Summit 2023" in Stockholm I am going to talk "next level curl" nordicapis.com/sessions/next-l…
30 minutes of fun #curl things brought in the last few years
Next Level Curl | Nordic APIs
During this talk, Daniel Stenberg will look at some of the most powerful and interesting additions to curl in recent years.Nordic APIs
curl 8.4.0 with Daniel Stenberg
Daniel walks through the significant security fixes, changes and bugfixes done in the curl 8.4.0 release.0:00 intro0:16 agenda0:52 release 2521:02 participat...YouTube
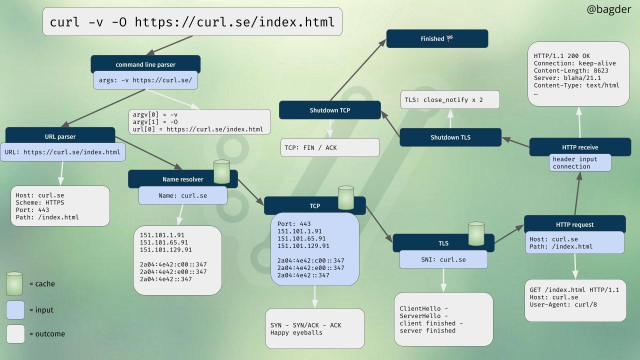
Why did the #curl #CVE202338545 vulnerability hide from static analysis tools?
The main reason for this is the type of code structure in question. In general state engines are quite difficult for static analysis tools, since as the name implies the state of the various variables depend on runtime state changes.
The code attempts to determine whether it is safe to use the provided host name for remote resolution. Since the code does not function correctly with host names longer than 255 characters, it falls back to using “socks5://” protocol (local name resolution) if the host name is longer. When the name is too long, the code forces “local name resolution” by setting “socks5_resolve_local” variable to TRUE.
Unfortunately this “socks5_resolve_local” variable isn’t stored in the “socks_state” structure as it should have been. For each state “step” the initial value for the variable is determined with:
bool socks5_resolve_local =
(conn->socks_proxy.proxytype == CURLPROXY_SOCKS5) ? TRUE : FALSE;
The INIT state then set the “socks5_resolve_local” to TRUE if the host name is too long:
/* RFC1928 chapter 5 specifies max 255 chars for domain name in packet */
if(!socks5_resolve_local && hostname_len > 255) {
infof(data, "SOCKS5: server resolving disabled for hostnames of "
"length > 255 [actual len=%zu]", hostname_len);
socks5_resolve_local = TRUE;
}
But this check is *only* done in INIT state. When the state is anything else, the initial value is used.
Now, later CONNECT_RESOLVE_REMOTE state checks if remote name resolution should be used or not:
if(!socks5_resolve_local) {
if (… sx->hostname is literal IPv6 address …) {
… use ipv6 address direct …
}
else if (… sx->hostname is literal IPv4 address …) {
… use ipv4 address direct …
}
else {
socksreq[len++] = 3;
socksreq[len++] = (char) hostname_len; /* one byte address length */
memcpy(&socksreq[len], sx->hostname, hostname_len); /* w/o NULL */
len += hostname_len;
}
}
As “socks5_resolve_local” flag is FALSE for the excessively long hostname the “socksreq” heap buffer will be overflown by the memcpy call.
There is no obvious way for the static analysis tools to determine that “socks5_resolve_local” might be set incorrectly for some of the states. Runtime #fuzzing will find this flaw quite easily, but unfortunately no fuzzing was performed for this specific functionality.

curlhacker - Twitch
I'm Daniel Stenberg, maintainer and lead developer in the curl project. I stream curl related stuff. Release presentations, curl development and related topics.Twitch