There are TLS servers that don't send the required close_notify alert message in certain conditions. #Google web servers do this if they think the that recipient isn't interested about the message body and no connection keep alive is set. Examples of such connections would be requests that end up with 0 byte message body while:
• HTTP/1.0 without "Connection: keep-alive" header or
• HTTP/1.1 with "Connection: close" header
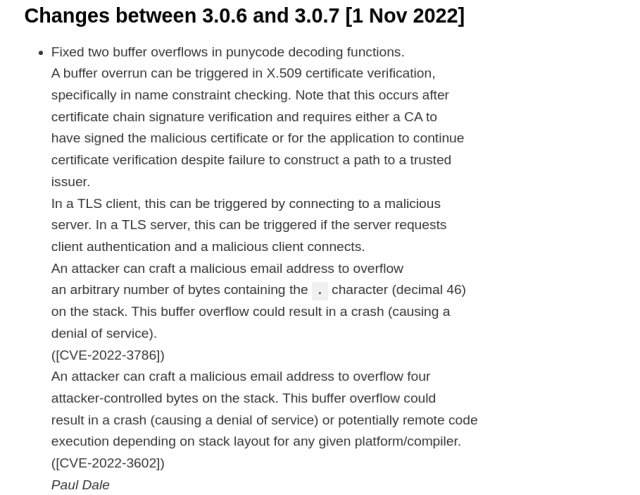
This can cause some complications since #OpenSSL 3 defaults to erroring out if the close_notify is missing.
SSL_OP_IGNORE_UNEXPECTED_EOF option was added to enable talking to these non-compliant servers. Enabling this option removes truncation attack protection - so this option should really only be used when absolutely necessary. However, unless if you control the servers being talked to, you probably need to enable this option for now.
So why does Google terminate connections without close_notify? Likely it is done to save some resources when tearing down TLS connections. If you have billions of connections going on all the time, even some small savings add up quickly.
github.com/php/php-src/issues/…
Description OpenSSL became more strict about unexpected EOF (not sending close notify) in 1.1.1e but reverted that change in 1.1.1f due to the huge amount of non-compliant servers. With the new maj...
GitHub