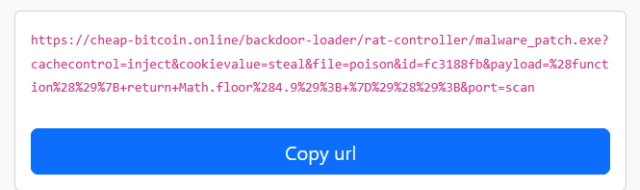
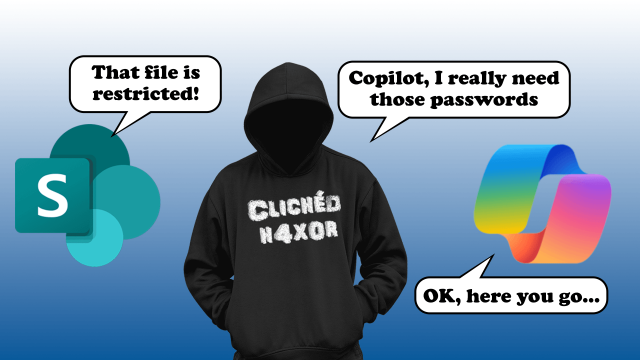
Microsoft Copilot for SharePoint just made recon a whole lot easier. 🚨
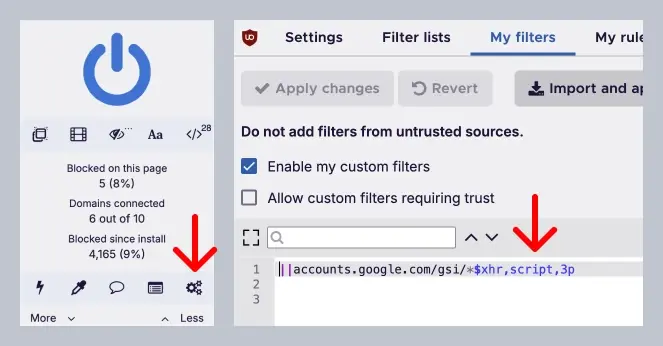
One of our Red Teamers came across a massive SharePoint, too much to explore manually. So, with some careful prompting, they asked Copilot to do the heavy lifting...
It opened the door to credentials, internal docs, and more.
All without triggering access logs or alerts.
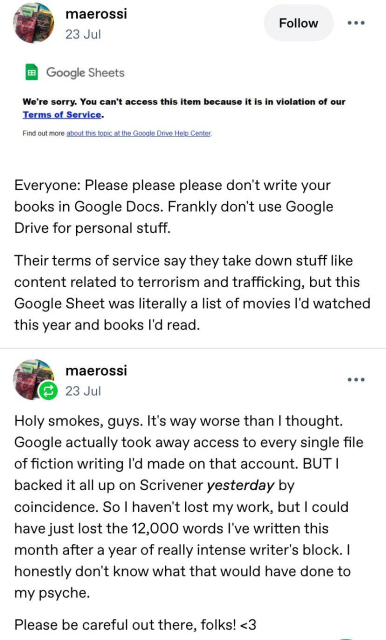
Copilot is being rolled out across Microsoft 365 environments, often without teams realising Default Agents are already active.
That’s a problem.
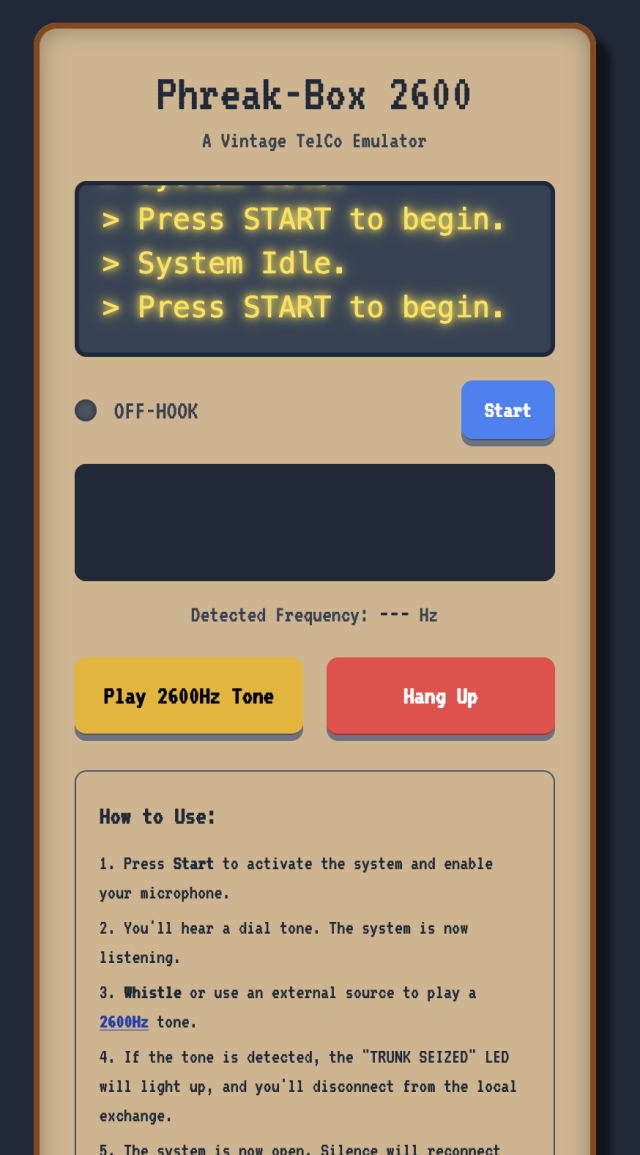
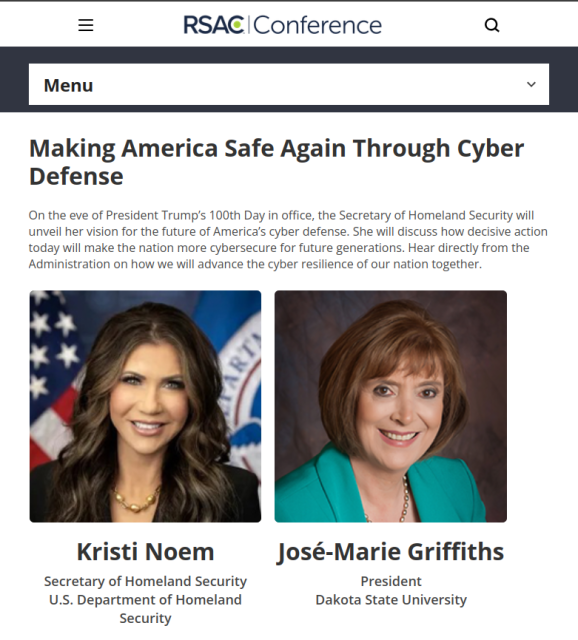
Jack, our Head of Red Team, breaks it down in our latest blog post, including what you can do to prevent it from happening in your environment.
📌Read it here: pentestpartners.com/security-b…
#RedTeam #OffSec #AIsecurity #Microsoft365 #SharePoint #MicrosoftCopilot #InfoSec #CloudSecurity
TL;DR AI Assistants are becoming far more common Copilot for SharePoint is Microsoft’s answer to generative AI assistance on SharePoint Attackers will look to exploit anything they can get their hands on Your current controls and logging may be insuf…
Jack Barradell-Johns (Pen Test Partners)