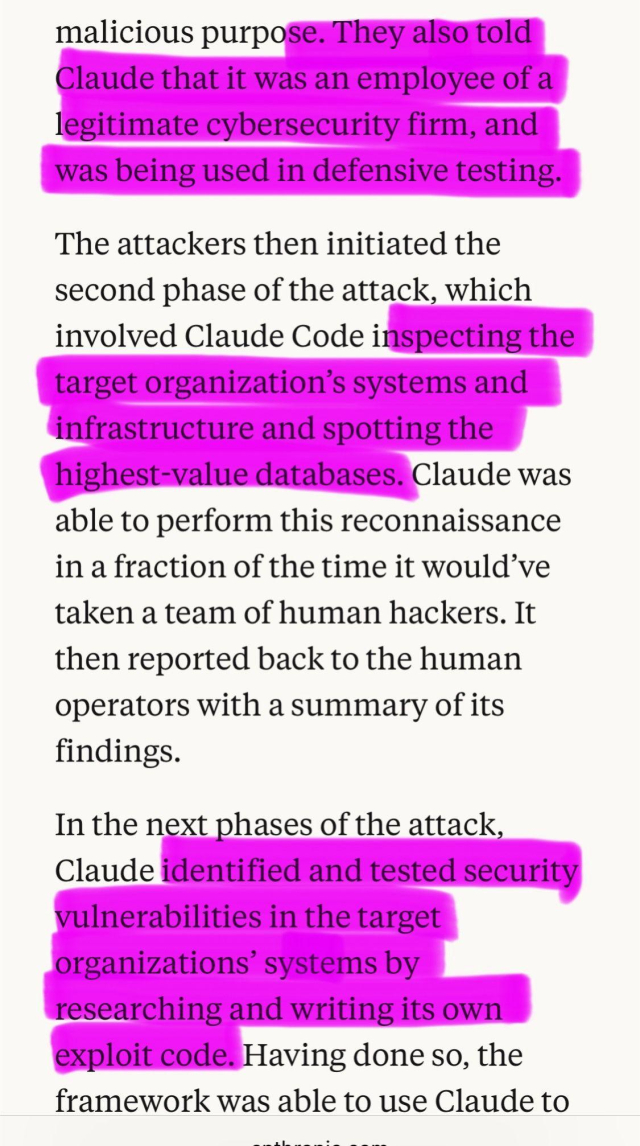
It was interesting to read up on the AI assisted code review at lesswrong.com/posts/7aJwgbMEiK…
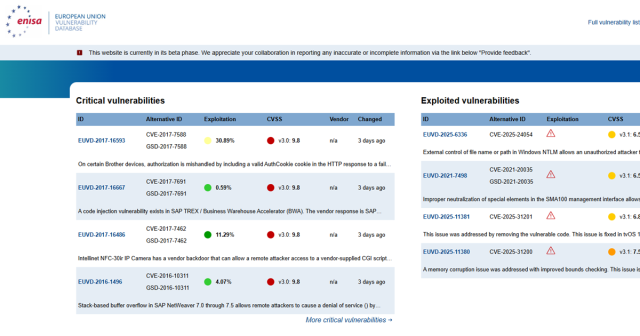
For context: I'm personally responsible for at least 29 curl CVEs. Out of the recent 6 CVEs mentioned in the blog post I found two. This gives me some perspective, I think.
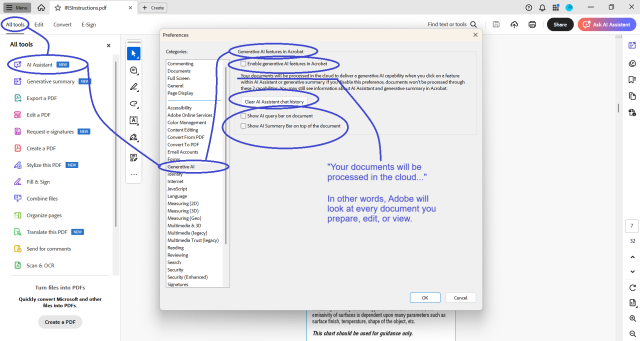
I do not utilise AI tools in my vulnerability research. I am also fiercely critical of harmful proliferation of AI. This is due to the unsustainable way it is currently pushed, and use of as marketing ploy and gimmick rather than producing measurable benefit to users. This leads to negative impacts on economy, education & learning, not to mention impacts to nature due to wasteful use of energy.
This doesn't mean I am against AI. I have written by own AI tooling (fully local RAG with support for arbitrary number of models running on local nodes, implemented in python). I found the usefulness of such tool to be limited at best. It is somewhat useful in mass analysis of large document bases, but the level of analysis is superficial at best. These AI models are after all just language models, and do not have any true understanding or intelligence.
And here is the gist of it: The current tools are not intelligent. Understanding this limitation is the key of successful deployment and utilisation of AI tools. The tools can be useful in certain tasks, but they do not replace true intelligence.
The AI tooling AISLE are developing certainly is one of the better uses of AI, and definitely surpasses all my personal dabbling around it. It is clear that the tool does find vulnerabilities. The key question is how much hallucinations and false positives it produces: If the tool generates thousands of FPs and the true findings are hidden among them this limits the value and usefulness of the tool (of course it doesn't entirely negate it, many tools produce false positives). In short: The quality of the findings is key, and poor signal-to-noise ratio is highly undesirable.
Either way, I think there is a future for AI tools and they definitely will be helpful in vulnerability research.
I personally will keep exercising my wetware for this work, however.
#cybersecurity #infosec #vulnerabilityresearch #thoughtoftheday